NetFlow is a Cisco proprietary protocol
the primary purpose of which is to collect all IP traffic on and send
the traffic as UDP packets to NetFlow collector server(or NetFlow
Analyzer). It helps Administrators to analyze network traffic and
generate reports on bandwidth usage, traffic volume, conversations
etc. It also helps in capacity planning to accommodate future growth.
Initially, NetFlow was introduced in
major Cisco routers and core switches to analyze traffic. With
growing business needs, more vulnerabilities arose due to security
threats on the network led to the birth Cisco Adaptive Security
Appliances also known as ASA.
With the facing off of Cisco PIX, it is
now an era of Cisco ASA with more enhancements. NSEL (NetFlow Secure
Event Logging) support in Cisco ASA helps analyze the traffic pattern
and allied security threats which was not available in the earlier
Firewall Device (PIX) that supported only Syslog analysis
NSEL reporting is different from
regular NetFlow, the NetFlow packets from the Cisco ASA are triggered
only when an event is created on the device. The event types that
trigger the NetFlow records are:
Flow Creation
Flow Denial
Flow Teardown
Enhanced Report:-
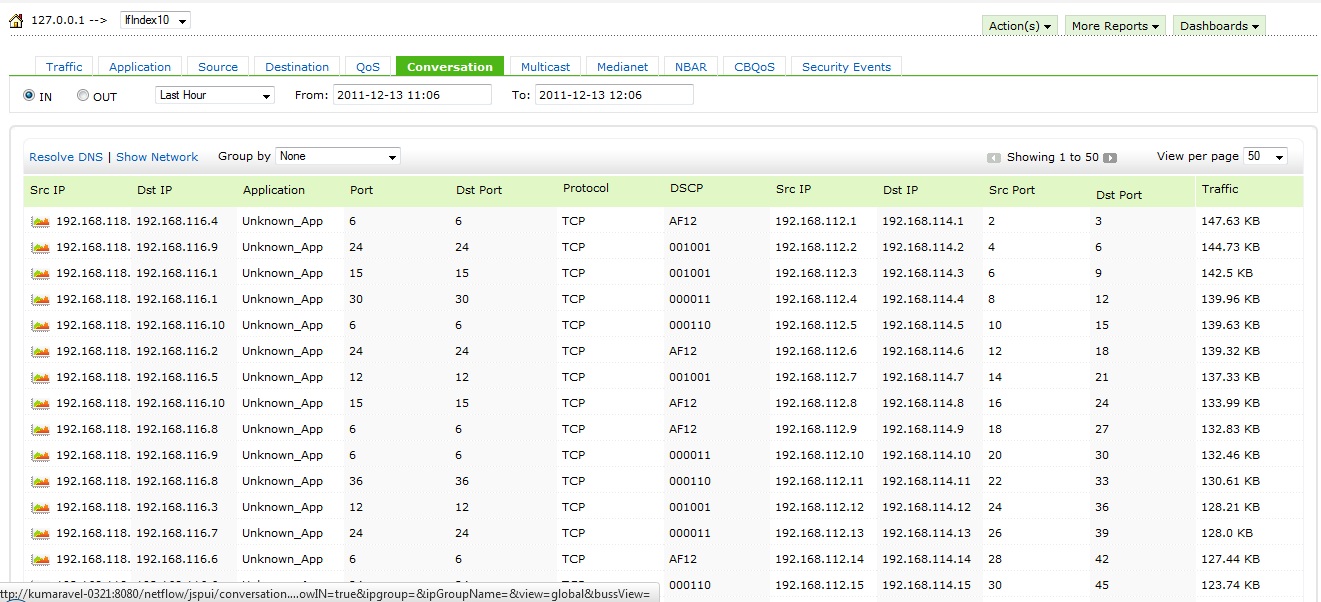
The Cisco ASA NetFlow reporting in
NetFlow Analyzer will show the traffic heading to WAN with their LAN
IP address as well their corresponding mapped NAT-ed IP address on
the Firewall.
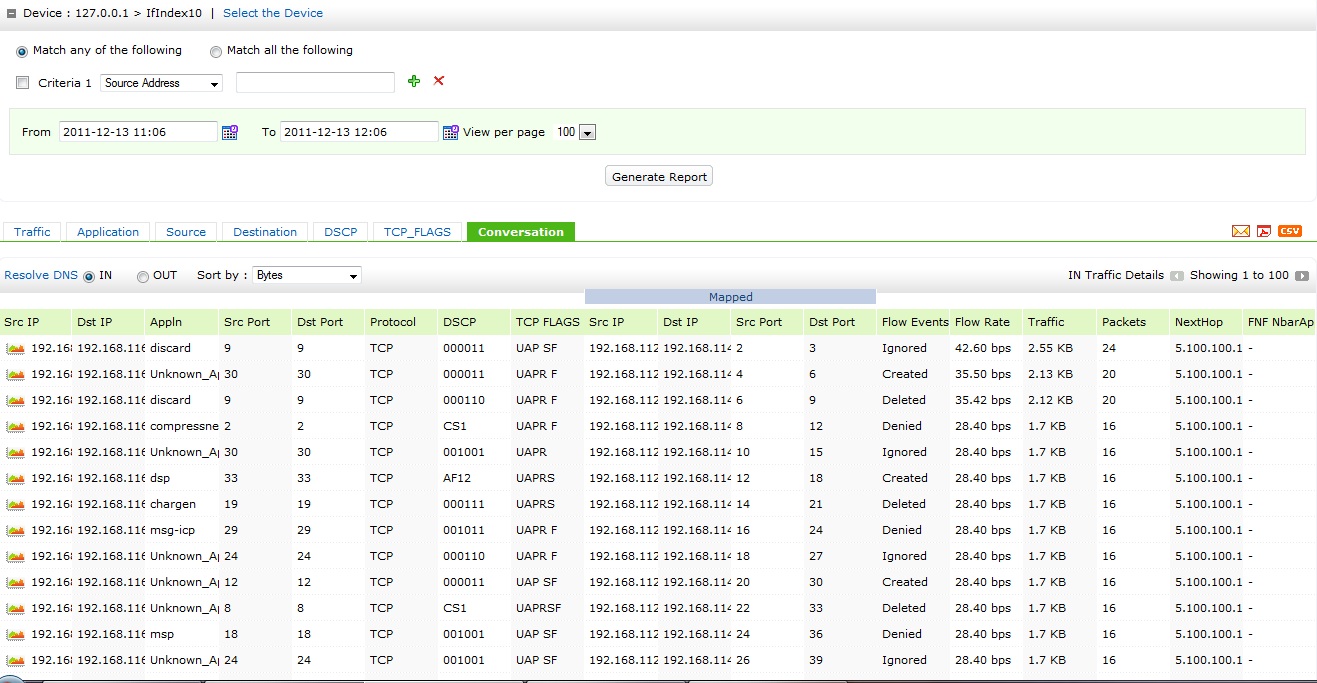
The troubleshooting report for ASA
interfaces will show the regular LAN traffic conversation with their
corresponding mapped NAT-ed IP address conversation for each
interfaces. The report will also show the Event types for each flow.
Points to ponder:
When it comes to Cisco ASA, NetFlow
packets are exported based on events triggered on the device and is
called NSEL (NetFlow Secure Event logging) which come with some
inherent challenges. The information from these NetFlow packets
cannot be used for complete bandwidth or capacity planning due to
certain differences with traditional NetFlow (ie. IOS NetFlow)
export. And these differences pose some limiting factors that one may
want to consider, like:
1. The concept of ‘active
time out’ and ‘inactive timeout’, which allows flow data export in a
timely manner from IOS devices, does not exist for NetFlow packets
exported from the Cisco ASA. This removes the possibility of
comparing NetFlow statistics with other bandwidth monitoring tools
which are based on timely polling for data.
2. NetFlow packets
exported from the device is based on events triggered on the device
(Flow creation, Denial of traffic etc).
3. The NetFlow packets
exported from the Cisco ASA includes bidirectional traffic
information which means that the return traffic of an initiated
conversation is not accounted as a separate conversation.
Hope there will be some more
enhancements to overcome the above said points in the near future. Click here to know how to configure ASA for NetFlow export.
For 30 Day Trial, click Download now.
Thanks and Regards
Praveen Kumar
You Can Learn More About the ManageEngine Product Line By Going to manageengine.optrics.com
The original article/video can be found at Enhanced Cisco ASA NSEL Reporting in NetFlow Analyzer

